Mostly tutorials which are some hard to understand or complicated in writing skip by the peoples, because of text tutorials only. But if we create a proper video by capturing our computer/laptop screen and upload the video with the tutorial, then it will become more comfortable to your visitors. We can describe anything which we perform on our computer to anyone by just making a proper video of our actions.
We use screencasting (screen recording) for making the video of our various tasks performed by us on our computer. By screen recording we can better describe/demonstrate our tutorial which is some how related to computer products or services. And by our screencasted video we can spread our tutorial in easy and fast way.
Today, I am going to share some great collection of screencasting (screen recording) software which are free to use and easy to handle. Here are the 10 best screen recording software.
CamStudio

CamStudio is an open source screen recorder software which can record every screen and audio activity on a computer & create industry-standard AVI video files or bandwidth-friendly Streaming Flash videos (SWF).
Operating system support: Windows
Jing

Jing can both take screenshots & capture a screen as videos. It is possible to add textboxes, arrows or rectangles to highlight spots.
It can send the generated outputs to Screencast.com, Flickr, a FTP account, Twitter & more.
With a microphone, you can record audio with the video as well.
Operating system support: Windows, Mac OS X
Webineria

This is a very easy-to-use open source software to create screencasts.
It records the screen as an .AVI file & offers an option to create .FLV file from it. With the help of hotkeys, it is possible to start-pause & stop recording.
A great feature is, it can combine another video input (like webcam) with thescreen recording process.
Operating system support: Windows
Wink

Wink is a tutorial and presentation creation software which can capture screenshots & enables you to add explanation boxes, buttons, titles & more.
It supports various output formats like .EXE, .FLV, .HTML, etc.
Operating system support: Windows, Linux
UltraVNC Screen Recorder

UltraVNC Screen Recorder is based-on CamStudio source with updates to improve the performance.
It supports both audio & screen capturing.
Operating system support: Windows
Windows Media Encoder

Windows Media Encoder is a powerful application for capturing audio and video content with high-quality multichannel sound, high-definition video quality, and support for mixed-mode voice and music content.
You may find this helpful: Getting Started with Screen Capture Using Windows Media Encoder.
Operating system support: Windows
BB FlashBack Express

BB FlashBack Express is the free version of some other advanced series. It can record from a video source, screen & audio.
It can export to AVI or FLV & has integrated support for direct uploading to the popular video sharing websites.
Operating system support: Windows
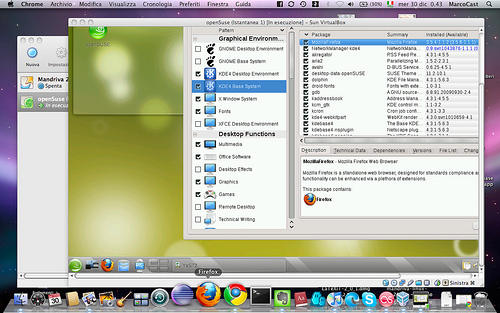
CaptureFox (Firefox add-on)

CaptureFox is a Firefox add-on which can record screens frame-by-frame to create tutorials. It also supports audio recording.
Operating system support: All major operating systems
uTIPu TipCam

TipCam, besides the standard screen recording with audio & video, has various features like:
- has AVI & FLV support
- audio can be re-recorderd
- beginning & end parts can be trimmed
- video can zoom to the mouse cursor with smart zooming
- ability to draw free-style during recording
Operating system support: Windows
Krut

This is a tiny Java application (works on many platforms) for creating screencasts.
Krut records movie files of selected parts of your screen in the quicktime mov format, including sound. The program has an intuitive and compact user interface.
Operating system support: All major operating systems












.jpg)

.jpg)