When we explore the virtual world must be familiar with the term BOT.
Bot is one of the clients are connected to an automatic system that does not directly controlled by humans. A bot to react to commands that are recognized by the action already known.
Bot is available in many formats, ranging from simple and that operates through a script on the server, up to a full and robust botyang.
I will not discuss here one by one type of BOT, but I will try to introduce one of the BOT DESKTOP that is only for entertainment only.
Why is the desktop boots, because the bot does not run on a server script like a bot, this bot is shaped desktop application and runs on personal computers, so if the computer does not run the bot will not run.
Bot the function I made up that this is the BOT is, where the bot will do some action like a facebook user to do, namely LIKE STATUS, STATUS to CONFIRM COMMENT Requests automatically. Maybe for those who have been using a version before is not so confused, because it's for a single bot bot is a development which I have previously made, of course, with some improvement-improvement.
Here are details on the new bot.
Application Name: FB GENERATOR AUTO COMMENT & LKE +
- Version: 4.1.3
- Release: July 19, 2011
- Facebook: https://www.facebook.com/vivekcreations
===== =============================================
1. LICENSE
================================================= =
- FB & Auto Comment Generator Like + is not a paid software (freeware)
- Abuse of the use will result in termination of service bot
=========================== =======================
2. Updates
================================================= =
- A new look and can be configured
- Confirm friend requests Auto
- Auto Logout of FB if the application is stopped
- Suport Systray
- Target can be selected
- the target exception (ID)
- Signature can be edited (if signature is fix)
- Fix: Comments repeated in the same shipment that makes spam
====================================== ============
3. USE
================================================= =
- connect to Facebook (Connect button)
- Login to your account via the browser in an application
- Settings
> Fill a comment (for Auto Comment)
> Check [Friend Mention] to call the friend's name in a comment
> To exclude someone from the BOT action, setting the expection
> Select the target bot




Bot is one of the clients are connected to an automatic system that does not directly controlled by humans. A bot to react to commands that are recognized by the action already known.
Bot is available in many formats, ranging from simple and that operates through a script on the server, up to a full and robust botyang.
I will not discuss here one by one type of BOT, but I will try to introduce one of the BOT DESKTOP that is only for entertainment only.
Why is the desktop boots, because the bot does not run on a server script like a bot, this bot is shaped desktop application and runs on personal computers, so if the computer does not run the bot will not run.
Bot the function I made up that this is the BOT is, where the bot will do some action like a facebook user to do, namely LIKE STATUS, STATUS to CONFIRM COMMENT Requests automatically. Maybe for those who have been using a version before is not so confused, because it's for a single bot bot is a development which I have previously made, of course, with some improvement-improvement.
Here are details on the new bot.
Application Name: FB GENERATOR AUTO COMMENT & LKE +
- Version: 4.1.3
- Release: July 19, 2011
- Facebook: https://www.facebook.com/vivekcreations
===== =============================================
1. LICENSE
================================================= =
- FB & Auto Comment Generator Like + is not a paid software (freeware)
- Abuse of the use will result in termination of service bot
=========================== =======================
2. Updates
================================================= =
- A new look and can be configured
- Confirm friend requests Auto
- Auto Logout of FB if the application is stopped
- Suport Systray
- Target can be selected
- the target exception (ID)
- Signature can be edited (if signature is fix)
- Fix: Comments repeated in the same shipment that makes spam
====================================== ============
3. USE
================================================= =
- connect to Facebook (Connect button)
- Login to your account via the browser in an application
- Settings
> Fill a comment (for Auto Comment)
> Check [Friend Mention] to call the friend's name in a comment
> To exclude someone from the BOT action, setting the expection
> Select the target bot
> Set the time interval
- Start
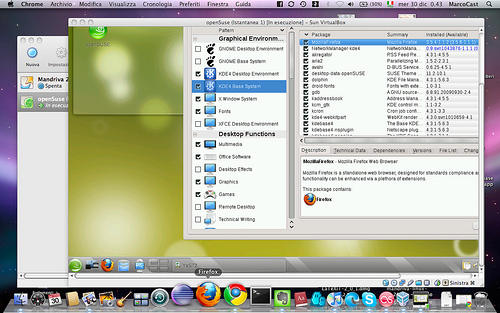
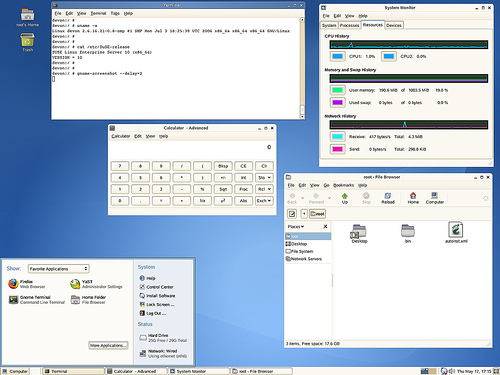
A. Front View

2. Display Settings
For this setting, the user can freely determine the action of bot, what your target and what comments will be sent.
- COMMENT: Textbox will be filled if we choose the action bot = Auto comment
- SIGNATURE: To provide a signature at the end of the comment.
- Mention FRIEND: For the name of a friend in the comments.
- KEY EXCEPTION: To set an exception.
- TARGET: Target bot ;)
- INTERVAL: Recurrence time it takes the bot to perform an action

3. Exceptions settings.
Click the Add / [+] and enter the ID facebook from friends who would be excluded
Click the Remove / [-] to eliminate the exemption
Kemudiaan click [SAVE] to save.

4. Bots can also be arranged through the Systray (hidden application conditions)

Note: All settings will be saved and loaded automatically when the bot is run.
Downloading Password: 123




.jpg)

.jpg)